JoomConnect Blog
reCAPTCHA: The First Line of Defense
When managing hundreds of websites for managed service providers (MSP), security is paramount. An MSP can’t preach strong security practices to their clients while having problems with their website. These days, hackers are aggressive and relentless when it comes to using exploits to test your security. So much so that even when applying multiple layers of protection across a site, the server, and keeping everything patched, threats can sneak in. This is why it is critical to have a first line of defense; in this case, a CAPTCHA.
 CAPTCHA stands for “Completely Automated Public Turing test to tell Computers and Humans Apart.” Its goal is to keep bots from accessing your forms. These bots can have two goals; one is to steal your SEO authority by creating backlinks from your site, reducing your SEO ranking, while increasing theirs. In the second variant, the bot seeks to exploit a weakness, gaining access to your website and once there, compromising your site.
CAPTCHA stands for “Completely Automated Public Turing test to tell Computers and Humans Apart.” Its goal is to keep bots from accessing your forms. These bots can have two goals; one is to steal your SEO authority by creating backlinks from your site, reducing your SEO ranking, while increasing theirs. In the second variant, the bot seeks to exploit a weakness, gaining access to your website and once there, compromising your site.
The second instance - the hack of their site - is what a fellow MSP was recently subjected to. Their website was so compromised, that Google listed it as a ‘hacked’ site. Imagine being number one in search results and underneath your title are the words, “this site may be hacked’. Talk about a business killer! After numerous attempts to mitigate the hack, they reached out to our team for assistance.
In troubleshooting their site, we noticed there were over 13,000 suspicious registrations. What was worse was the majority of the entries weren’t limited to fake names, they were also hyperlinks, which once clicked, would expose their systems to intrusions. This is, of course, what one of their team members accidentally did, exposing the business.
The question to ask is how were 13,000 false entries from a foreign country allowed to register in the first place? The simple answer is there was nothing in place to stop them. No permissions, exclusions, or requirements were placed before a visitor could register. No first line of defense. Of course, most website owners know that the solution to prevent the spamming of forms is having a CAPTCHA in place. They just don’t want to use one, mainly because - and let’s be honest - out of fear of turning off potential customers, which is a valid concern.
The reality is, most website developers know that a CAPTCHA can increase your bounce rate and generally reduce your opportunities for engagement. Simply put, a CAPTCHA can be yet another roadblock to conversion. A 15% bounce rate (in addition to the existing bounce rate, is nothing to ignore) due to a CAPTCHA isn’t unusual, and low bounce rate is critical to engagement and conversion opportunities. So this MSP needed to make a trade-off: open access to their registration forms, or install a CAPTCHA and potentially reduce their opportunities for traffic and conversions. They decided that they would rather have more customers and manually clean out the spam. What they didn’t count on was how vulnerable it would leave their business.
 That being said, their concerns were valid and fortunately, Google recognized the reduction of business opportunities due to using a CAPTCHA. In 2013 Google revised and updated the CAPTCHA format. This version, known as reCAPTCHA, came in three formats:
That being said, their concerns were valid and fortunately, Google recognized the reduction of business opportunities due to using a CAPTCHA. In 2013 Google revised and updated the CAPTCHA format. This version, known as reCAPTCHA, came in three formats:
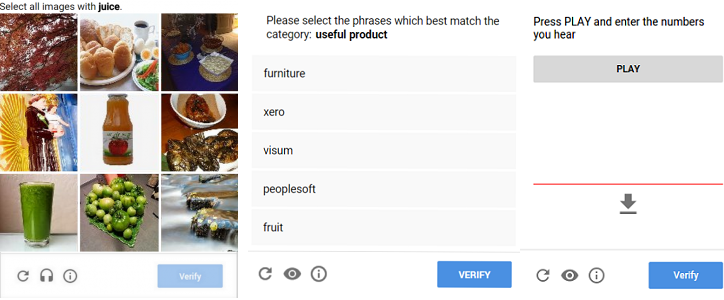
- Image Challenge: you select related images from a set. (i.e., select images with juice)
- Audio Challenge: enter numbers that are read out loud.
- Text Challenge: pick all the phrases that match a given category.
While more intuitive than the original CAPTCHA, the first generations of reCAPTCHA could still slow down user interaction and negatively affect user experience. This led Google to refine it to the NoCAPTCHA reCAPTCHA, represented by the current “I’m not a robot” checkbox we’ve all come accustomed to seeing when completing forms on modern, up-to-date sites. Significantly less intrusive than previous versions, this new reCAPTCHA has been widely accepted by the majority of developers and users alike. The more straightforward interface reduces the frustration that occurred with all earlier versions of CAPTCHAs and a less frustrated visitor to your website is more likely to stay longer and convert.
The future is invisible.
Google’s latest development in CAPTCHA technology is what they call ‘invisible’ reCAPTCHA. Invisible because, according to Google, they have refined their algorithms to such a level that it can tell you’re a human or bot by how you interact on a webpage and block the bots. What’s different about this version of reCAPTCHA is that it is done behind the scenes, with no user interaction required. In fact, as of this writing, Google isn’t sharing exactly how this reCAPTCHA works, only that it does, reducing at least for now the ability for hackers to get ahead of it.
Perfect is the enemy of the good.
One thing to note: CAPTCHAs are great for stopping bots, but not so good for stopping fake accounts from being created by real live humans, so it is not a perfect solution. However, many spammers will use bots to spot weaknesses in your defense before deciding to invest the resources to take advantage of them. With a CAPTCHA in place, the hacker may assume you have other security protocols in place and move on to easier pickings. In other words, anything that can slow down or even prevent the initial probe from being successful has value and should be embraced, even if it’s not 100% perfect.
Your sales, marketing, and even your SEO consultant may push back on the inclusion of a CAPTCHA due to fear of negative user experiences. However, with Google’s current reCAPTCHA, which is typically compatible with most modern websites, it remedies the roadblock while still providing protection. Older sites, using technology from a few years ago might not be built to simply drop-in reCAPTCHA.
For assistance with developing a plan to address your customer’s concerns regarding best practices or just how to better position yourself and your expertise as a MSP, don’t hesitate to contact us. We have a wide ranges of solutions and services designed to provide your business with the tools needed to break away from the pack.




Comments